


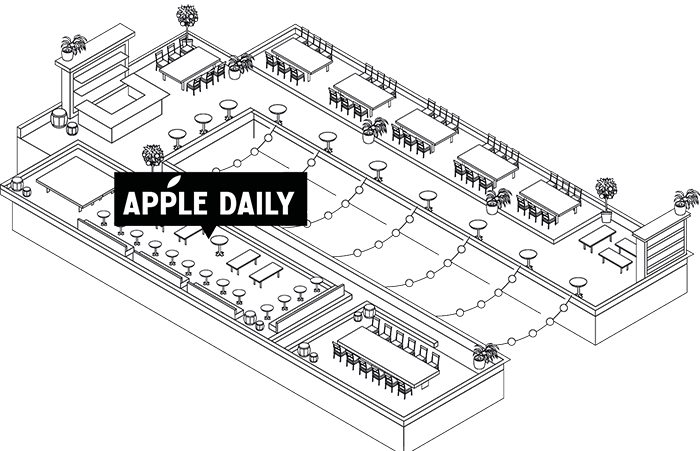

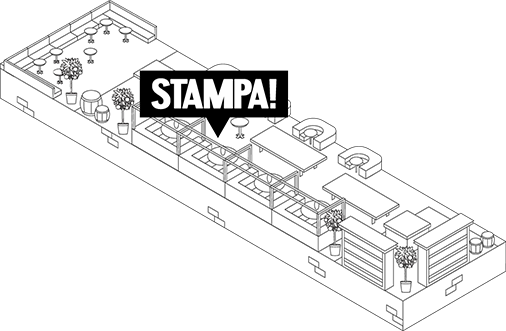
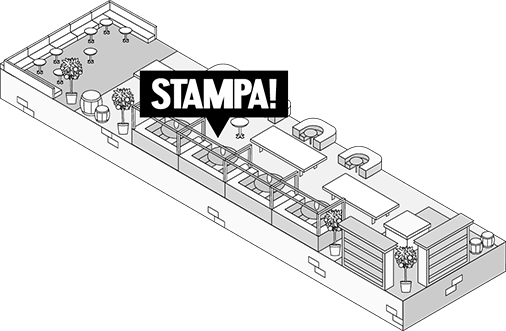
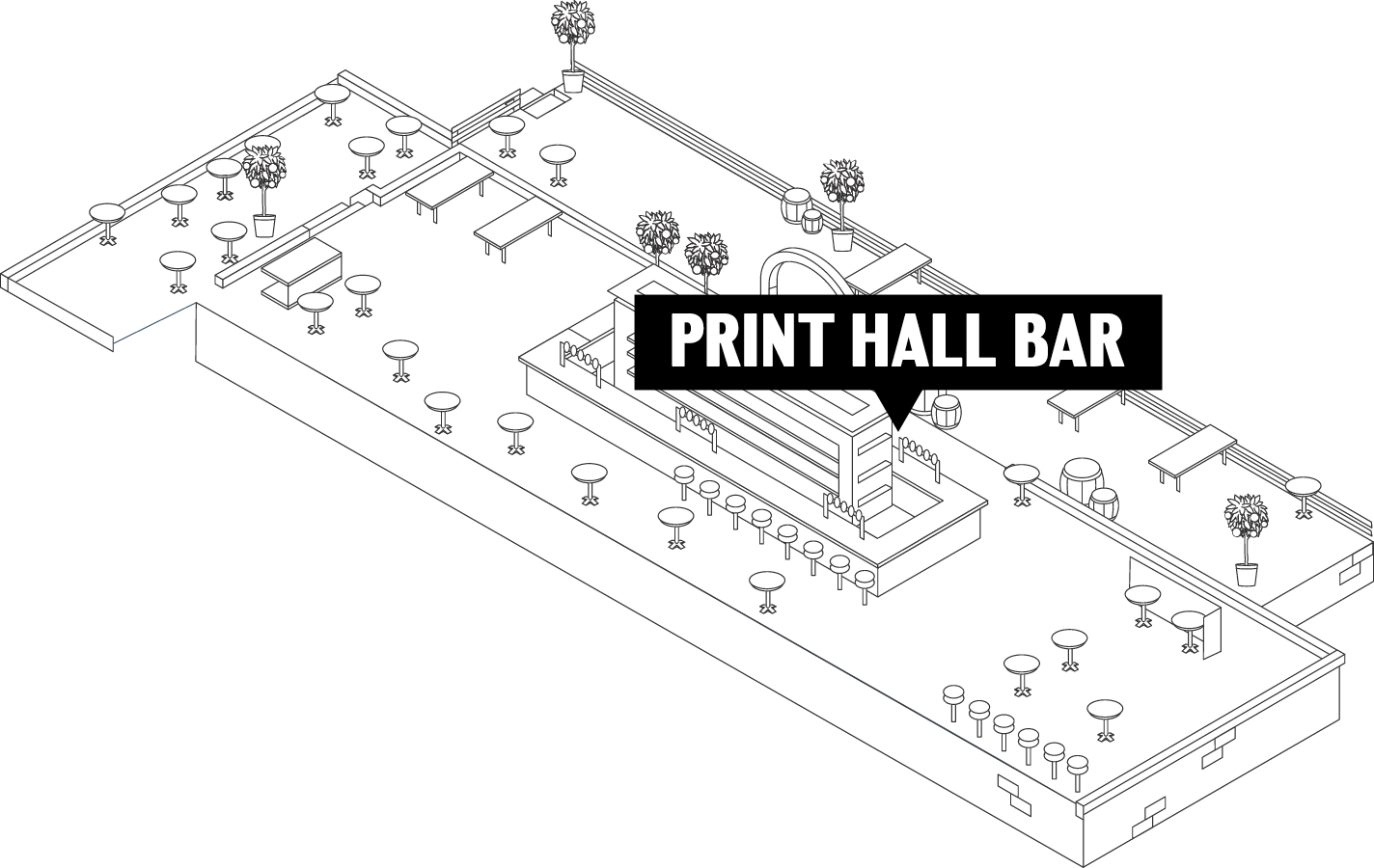

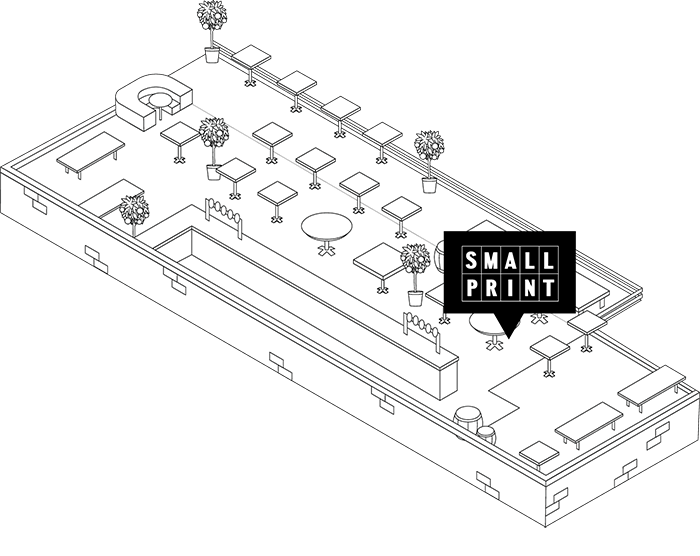

Allow your guests to immerse themselves in the versatility of Print Hall precinct's function and event spaces. From the convivial Paper Boy Booths, perfect for gatherings of 10, to the grandeur of reserving the Chairman’s Boardroom or the entire Hall for up to 900 guests.
Learn MoreGIVE THE GIFT OF AN UNFORGETTABLE EXPERIENCE IN THE HEART OF PERTHS PREMIUM FOOD AND BEVERAGE PRECINCT.
THE PRINT HALL GIFT CARD ALLOWS RECIPIENTS TO EXPLORE THE PRECINCTS PREMIUM RESTAURANTS AND BARS.